-
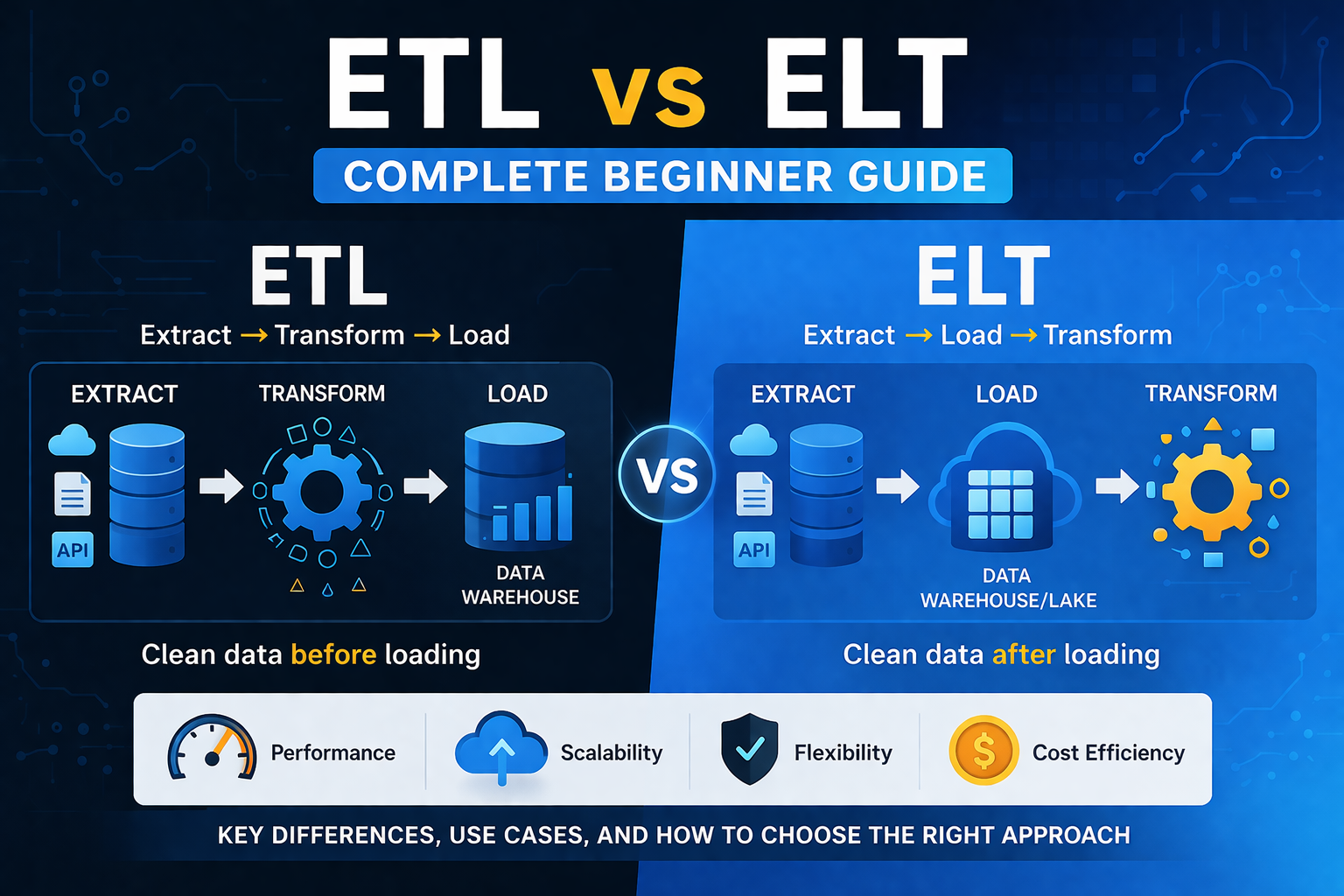
ETL vs ELT! In today’s data-driven economy, businesses generate massive amounts of data from apps, websites, sensors, and customer interactions. But raw data alone is not useful. It needs to be cleaned, organized, and transformed into insights. That’s where ETL and ELT come in. If you’re new to data analytics, data engineering, or business intelligence,…
-
Top 10 AI Tools for Business in 2026? If you run a business today, you’ve probably heard the same thing everywhere: “Use AI or get left behind.” That’s partly true but what most people don’t tell you is this:AI only works when you apply it to real problems. Too many businesses sign up for multiple…
-
Data analytics for beginners with no tech experience! There’s a quiet shift happening in the job market. You’ve probably seen people moving into tech roles without traditional degrees, landing remote jobs, or talking about “data” like it’s the new gold. And somewhere in the middle of all that noise, you might be wondering: “Can I…
-
Cloud Security in 2026: Securing Multi-Cloud and Hybrid Environments Without Increasing Risk. Cloud adoption is no longer a strategic experiment. By 2026, most enterprises operate in a multi-cloud or hybrid environment combining services from providers like Amazon Web Services, Microsoft Azure, and Google Cloud, alongside on-premises infrastructure.The promise is agility, scalability, and resilience. The risk,…
-
Cloud spending is no longer a background IT expense. For many digital businesses, it is one of the top three operational costs. Yet most organizations still manage cloud budgets using spreadsheets, static trend lines, and end-of-month reviews. By the time finance flags an overrun, the money is already spent. AI-powered cloud cost forecasting is changing…
-
Identity Is the New Perimeter: Why IAM Is the Foundation of Zero Trust in 2026? Since the turn of the decade, cybersecurity has undergone a profound shift. The traditional model of perimeter defense anchored in hardened firewalls and network boundaries was once considered sufficient for enterprise protection. Yet, as organizations increasingly adopt cloud platforms, support…
-
Zero trust architecture in the age of modern Cybersecurity: In a world where digital infrastructure spans cloud services, mobile endpoints, remote workers, and increasingly sophisticated cyber threats, traditional perimeter-based security models no longer suffice. The rise in breaches, lateral movement by attackers, and data exfiltration incidents highlights the need for a fundamentally different approach to…
-
How AI is transforming cybersecurity?. A breach would occur, analysts would investigate, patches would be applied, and organizations would move on until the next attack. Today, that model no longer works. Attack surfaces are expanding across cloud environments, remote work setups, SaaS platforms, APIs, and IoT devices. Threat actors are faster, more automated, and increasingly…
-
AI in cloud computing is no longer experimental. It is operational, measurable, and directly tied to business performance. In 2026, organizations are not asking whether to use AI in the cloud. They are asking: This article breaks down real-world use cases across SMEs, enterprises, and technical teams focusing on practical implementation, not hype. Why AI…
-
Cloud cost optimization is no longer optional, it’s foundational. Yet one of the biggest challenges organizations face today isn’t migration but it’s cost control. From startups to enterprises, many businesses overspend on cloud services without realizing it. Unused instances, poor architecture, and lack of monitoring can inflate bills dramatically. This guide breaks down practical, real-world…